Introducing DCA 4: revolutionizing Print Fleet Management
Data Collection Agent version 4 (DCA 4) sets a new standard for printer fleet management, delivering unparalleled security, efficiency, and reliability.
In addition to all the eXplorer 3 features (clustering, SDS, Auto Update, etc.), it brings forth groundbreaking functionalities and capabilities, including:
- Real-time Connection: Utilizing MQTT, a lightweight IoT communication protocol, DCA 4 enables direct, real-time communication between users, agents, and devices, bolstered by HTTP/2 – GRPC for traffic optimization and SSH for remote device access.
- Device Web Access: Access printer web pages from anywhere on the internet without the need for remote network connections, ensuring seamless navigation across all printer brands and models.
- Multi-Platform Functionality: Offering a unified experience across Windows, Mac, Linux, and Raspberry platforms, Data Collection Agent version 4 ensures consistency and accessibility across diverse environments.
- Granular Data Collection: Customize data collection types and frequencies to optimize efficiency and ensure real-time management.
- Optimized Network Discovery: Redesigned discovery processes enhance stability and troubleshooting, simplifying operations in critical network environments.
- Enhanced Security: Built with a security-by-design approach, DCA 4 mitigates risks and supports SNMP v3 and device authentication for maximum security.
- Improved Supportability: Streamlined troubleshooting processes reduce reliance on customer intervention, expediting issue resolution and enhancing convenience.
- PaperCut Integration: Seamlessly integrate with PaperCut MF/NG instances for enhanced business intelligence capabilities at no additional cost.
OS requirements
Windows
DCA 4 is supported starting from Windows 10 version for clients and Windows Server 2016 for server installation. For older operating systems, only DCA3 is supported.
Its setup will verify the .NET core libraries installation and will download the necessary libraries from the Microsoft website.
The Data Collection Agent installs two services, MpsMonitor.Dca.Client and MpsMonitor.Dca.Monitor, that use the system Network User and Local User accounts respectively.
If there are special restrictions or policies that prevent the activation or the service execution by the above accounts, it will be necessary to use a specific local user instead.
The DCA installation procedure will assign to this user the minimum rights needed to perform the service.
MacOS
DCA 4 can be installed from MacOS Mojave 10.14 or later and can be installed on Intel or Arm (M1,M2) CPUs.
It is necessary to install .NET core 6 SDK (Intel and Arm version) before installing the DCA4.
Linux and Raspberry
DCA 4 can be installed on Linux distributions that support .NET Core. Can be installed on Debian 11, Ubuntu 18.04,20.04,22.04, Raspberry PI OS 32bit/64 bit.
It can be installed on the following Raspberry boards:
- PI2 board (32bit)
- PI3 board (Model B) (32bit)
- PI4 board (64 bit).
Should you have any questions or need any information about older versions of the DCA, please don’t hesitate to contact us.
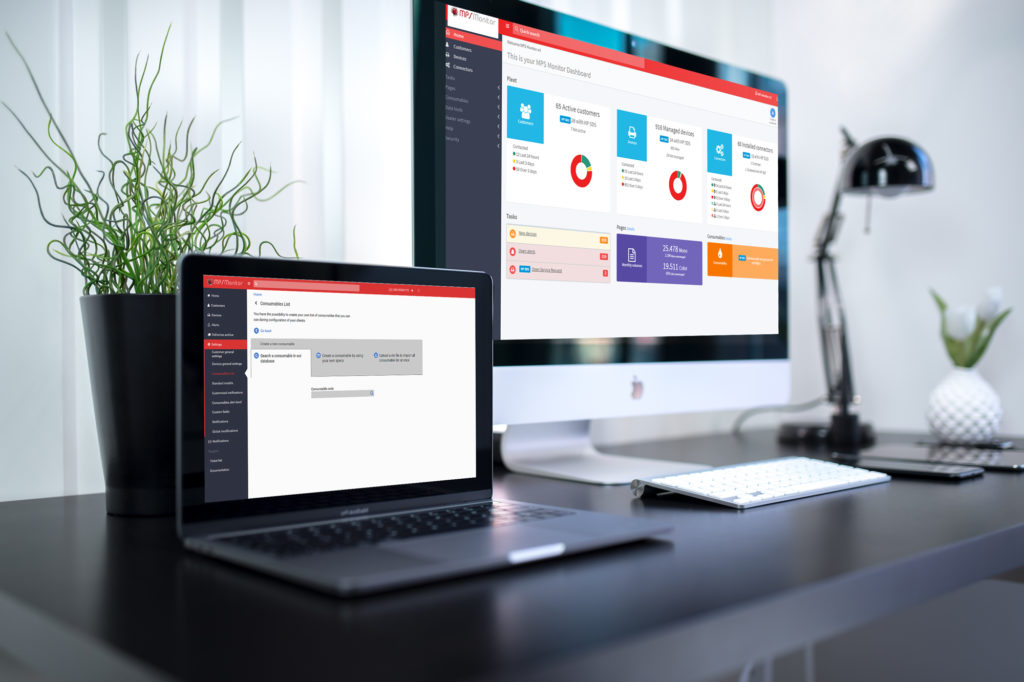
Try MPS Monitor for free on your fleet
MPS MONITOR IS A PARTNER OF
CERTIFICATIONS